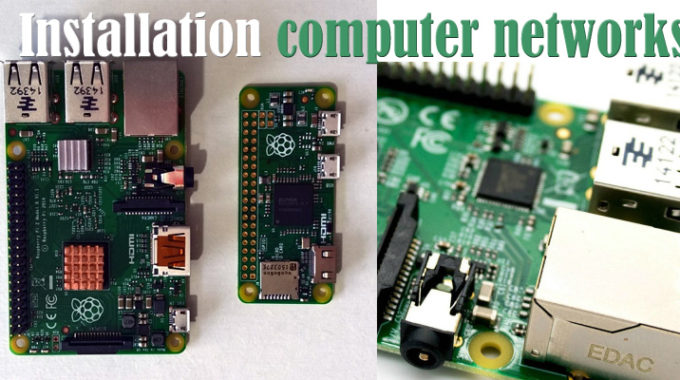
Pc Network Installation computer networks basics tutorials point
introduction to computer networks and cybersecurity pdf download Voice cabling and information cabling are the principal roots of every personal computer operating effectively on a distinct network. A master’s degree system teaches an individual about industry procedures and about theories that allow investigation to advance the field. Specialized instruction includes studying how to style databases and handle other personnel. Designing virtual private networks and laptop architecture are some of the accessible study choices. Topics center on how to implement information theory, digital image transmission, and optimization. Doctorate study is also available for men and women that have a need to turn out to be a professor or advanced designer.
Layer 2: Data Link: Includes the Network Interface Card (NIC), which serves as the interface amongst the pc and the network. The NIC is typically built into the motherboard and is assigned a Media Access Handle (MAC) address that offers each …