Why Should You Use Enterprise Private Networks?
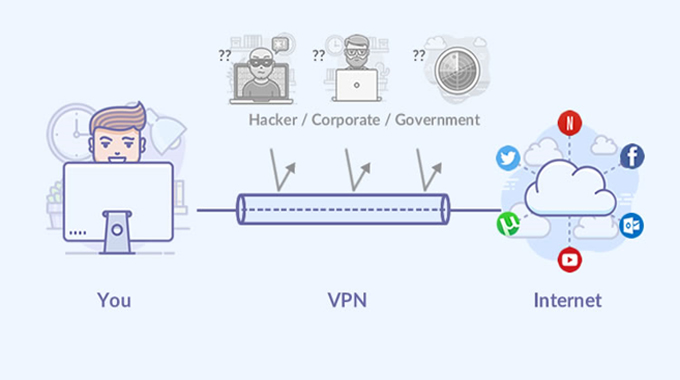
Enterprise Private Network is a portion of network basics that is responsible for some important functions and its usage is also very much widespread. Enterprise Private Network is a kind of public network and has the same functions like any other public network. However, it is protected by more advanced security processes and it is designed to carry out confidential corporate data. Enterprise Private Network is often compared to switches and in the following few lines, I am going to highlight the benefits of such a concept.
It is considered an important element of corporate infrastructure and it offers several advantages. The most important one is, the enterprise private network helps in managing, protecting, and monitoring the private data of the organization. There are several reasons behind its popularity. First of all, these private networks are specially designed to provide better security to corporate data. Second, these networks are designed …