computer networks a systems approach 5th edition pdfAt its most simple, a pc network is numerous computer systems that have been connected. Account Management is responsible of undertaking diverse tasks, for example: sorting out the usernames such as enabling and disabling the proper of access and they would manage the user access to the personal computer. Service account management would want to retailer all of the networks accounts in a kind of a extended list when the all accounts are stored, the server would be capable to change the service password and then all of the accounts would be updated. An account management would also hold files and documents which a certain user have stored.
The easiest way to want somebody a birthday these days is to send them birthday wishes via social networks or messaging apps. There are a lot of websites supplying these wishes, but hardly ever are they original If you invest some time on it, I am sure you will find precisely the birthday wish you need to have. Even so, anybody can send a birthday image. Are you prepared to do far more than that? If so, listen to my suggestions on how to be distinct in your birthday wishes, depending on who you send them to.
A router is an really diverse classification. Routers may possibly provide connectivity inside offices, between various places, and among companies and the Internet. The biggest routers connect Web service providers, are used in quite huge organization networks, or connect a business with a satellite hyperlink to a distant corporate locale. Advanced routers are effective computer systems, comprehensive with microprocessors. Quite sophisticated routers are employed by the World wide web to handle the network site visitors most efficiently.
What Is Laptop Science And Engineering?introduction to computer networking concepts
computer systems and networks plymouthThe makes use of of computer systems nowadays are as diverse as the types of computers that exist in the industry. IT specialists maintain up with recent trends in contemporary technologies and have the capability to recommendations on efficient and modern innovations to boost the company Good computer assistance specialists will certainly not only fix your hardware and software application difficulties yet will surely give certified assistance to boost your firm.
A wireless network is a lot simpler to set up today. Most all network devices can be identified in both wired, and wireless. A wireless device may well cost a tiny more cash, but you are getting the flexibility of moving your computer networking devices anywhere within the property. The benefit of becoming in a position to do that is enough for most people to pay the further income for every device.
When computer systems and Internet became commonplace beginning in the 80s and 90s, customers rushed out to seek info by way of surfing by way of browsers like web Explorer, Yahoo and Google. There are two major sorts of the laptop network client-server and peer to peer. In the client server computing, a laptop plays a major function recognized as server, where the files, information in the form of net pages, docs or spread sheet files, video, database & sources are placed.
Network refers to your computer’s network interface. If you are wired into your home’s network, it would be named the Ethernet adapter. Nevertheless, if you are using a wireless access point, then you are employing a wireless network Interface. Most individuals just contact this WiFi interface. The speed of the network is measured in Mbps (or mega bits per second). Most Ethernet adapters run at one hundred Mbps, and even 1000 Mbps. Wireless speeds differ. It can be anywhere up to 300Mbps. If your wireless signal is poor, it can do down as low as 1Mbps.
five. Computer Support Specialists: Technical help for customers is important. Specialists in this region can perform for a non-IT business in their support department or for a firm that specializes in supporting other businesses in outdoors industries. Some companies demand a bachelor’s degree in computing, other individuals accept associate’s degrees or certificates and relevant work expertise. Median salaries in 2007 had been $42,400.
Ultimately the word got out and the systems came back online. Within a few days items were mainly back to regular. It is estimated that the Morris worm infected a lot more than six,000 computer systems, which in 1988 represented 1-tenth of the Net. Despite the fact that none of the infected systems have been actually broken and no information was lost, the charges in program downtime and man-hours were estimated at $15 million. Victims of the worm integrated computer systems at NASA, some military facilities, several significant universities, and healthcare investigation facilities.
The major function of program computer software is to handle and regulate the functionality of the hardware elements in a pc. It frees applications from low-level abstraction such as transferring information from memory to disk or rendering text on show. Program software generally consists of the operating method, such as Windows, Linux or UNIX and utilities such as file managers, text editors and disk formatters.
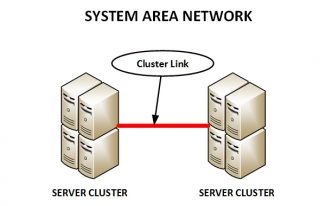
Computer network engineers function to set up, manage, and repair laptop networks. Professionals perform with a selection of different networks primarily based on what career they are in. The most widespread networks include neighborhood location networks, which are utilised to connect limited areas like buildings or properties. Metropolitan region networks hyperlink a huge region like a college campus and wide region networks are set up nationally and internationally. Job responsibilities vary depending on what variety of network they are operating with. Career work entails a large quantity of activities like installing hardware, monitoring network usage, suggesting solutions to network difficulties, and designing networks. All of these places and much more can be learned from online schooling. The more advanced a degree is the a lot more duty and work a student will be capable to handle upon completion of a system.
Introduction To Laptop Networking computer networks a system approach 4th edition
introduction to computer networking bookAlmost all businesses and organizations would cease to run effectively if their pc system crashed or had issues. For setting up a computer network, you need to understand many standard terms. Utilizing switches, hubs and cables in a pc network is common but to acquire maximum efficiency, the proper type of devices and cables are required. The cables are distinct from one an additional in terms of speed for transmission of data, reduction of crosstalk and modes of installation. Uncover answers to your Regularly Asked Concerns (FAQ’s) about distinct kinds of networking cables and their utilizes.
Wireless Technology today, are robust, effortless to use, and are transportable as there are no cables involved. Apart from regional location networks, even Metropolitan Region networks have started employing Wireless technologies (WMAN). Aviation, Transportation and the Military use wireless technologies in the kind of Satellite communications. Without making use of interconnecting wires, wireless technologies are also utilised in transferring power from a power source to a load, provided that the load doesn’t have a constructed-in energy source.
The printer ought to be connected to the network printer port or to a laptop with a USB cable, then plug in the power cable for the wireless network printer and turn on the printer itself. From this point it will be needed to comprehensive this approach of installation on all the linked computer systems inside the network. This process may possibly vary somewhat, but in common this it is comparable to all networks. If the wireless network printer is a multifunctional device it perhaps essential to share such functions as scanning across the network. This will permit all computers to use this functionality, but keep in thoughts that they could have to wait in line or queried for access.
There are also a few security limitations which hackers can exploit to result in harm in a wireless network. But Wireless technologies with far better security attributes have began to come out. So this is not going to be a problem for lengthy. Speaking of progress, Wireless technologies is not restricted to effective computer systems and mobile handsets. The technology has progressed adequate that Wi-Fi enabled TVs and microwaves have began appearing in the markets. The most recent and the most talked-about wireless technologies is the NFC or Near Field Communication, which lets customers exchange data by tapping their devices with each other. Making use of wireless technologies are not as costly as it employed to be in the last decade. With every single passing year, newer and better wireless technologies arrive with greater advantages.
Computer and info technology remains a key organization expenditure in terms of initial investment and continuing upkeep charges. Company leaders must continually evaluate the pros and cons of when to adopt the most current technologies. Integration can bridge the gap among older legacy systems that continue to function and newer technologies that have been created along the way.
However, this is far from the only setup in residence networks. As much more and far more peripheral devices are manufactured to make use of wired and wireless residence connections, far more and far more consumers are able to advantage from streaming media. For instance, a new HDTV may connect to the difficult drive and permit home customers to watch videos or appear at family members images. Other folks may well select to use these systems to stream games, to facilitate on the web chat or email by way of their Television or to download new entertainment by way of a Blu-Ray player or other connected device.
I have currently joined the doctoral plan in laptop and information technology at UoP, could you please send me newest PhD subjects in the field of AI, ANN, Cryptography and Network Safety? Also your guidance for narrow-down in the location of interest will be appreciated. The specialized aspect of an investigation is sub-categorized into four main places pc forensics, network forensics, database forensics and mobile device forensics. The actual physical procedure involves acquiring evidence, forensic imaging, analysis and reporting proof.
3. A Wireless sensor Networks(WSN). Why should customers be concerned if their computers are infected by rootkits and develop into botnets? The answer is the damage that their infected systems can do. two. The job description can be utilised in any business where computers play a vital part in its company operation. They can design and style new systems to meet evolving business needs, and also assist sustain and boost these set-ups.
Subjects In Computer Science (Data Technologies)computer networks development
computer networks a systems approach 5th edition solution manual pdfThe firewalls are the network safety devices that preserve the networked pc secure and secure. Gateways are devices which connect two are far more networks that use diverse protocols. They are related in function to routes but they are much more potent and intelligent devices. A gateway can in fact convert information so that network with an application on a computer systems on the other side of the gateway e.g a get way can get email messages in 1 format in convert them into another format. Gateway can operate at all seven layer of OSI model. Since Gateway carry out data conversion so they are slower in speed and very expensive devices.
The larger the bandwidth, the better the transfer of info. Bandwidth is the data transfer capacity of the network system in the given time frame. As compared to the CAT5 cables, the bandwidth of CAT5e cables is much greater. Due to its greater bandwidth, CAT5e supports Gigabit Ethernet networks. If you have a 100Mbps switch, CAT5e cables are more suitable than CAT5.
Understanding a company’s pc program can be beneficial in increasing the productivity of the firm and can eliminate extended periods of downtime, even if you sooner or later have to get in touch with outside laptop repair technicians to troubleshoot your company’s pc network. Qualifications for laptop operators can differ, but they can contain standard expertise of laptop operating systems, on the web or handle panel repair tools, standard cabling, router and hardware troubleshooting, along with numerous proprietary and office application applications.
The simplest way is peer to peer. This is where two or much more computer systems are hooked up directly to every other. In other words if you have five computers you would have computer 1 hooked into personal computer 2 which would be hooked into computer 3 and so on. In this variety of connection each and every pc is dependent on the other. So if computer 3 would go down then computer systems 1 and 2 would not be in a position to communicate or exchange details with computers 4 and 5 and visa versa. That is the principal problem with a peer to peer network. Also in peer to peer networks the write approach amongst computer systems leads to data corruption issues. This is not something they teach you in college but some thing you discover from experience.
Mainframe computer systems are massive computers that have a assortment of networks terminals making it feasible for much more than 1 user to operate on it at the same time. Mainframe computer systems are quite pricey to purchase and keep. The Central processing unit and the computer memory were housed in a large cabinet from which the term mainframe computer” was coined.
We all know that a browser is essential to run the internet on a pc. A internet browser is a kind of software that functions to open a webpage. A good internet browser is the 1 that does not take significantly time to open the site and is fairly easy to use. When installed on a client laptop, computer software is retained in non-volatile memory typically identified as disk drive. When the pc is powered up, nevertheless, the operating system and all running applications, are temporarily loaded onto principal and volatile memory recognized as random access memory (RAM).
Doom worm (released in January 2004). According to the Web Security Alliance information, a single out of 3 small organizations was impacted, whilst only one out of six enterprises was impacted. It is not always private. As you will find out later, most attacks and security threats are aimed at the common public and not directed at any distinct firm or network. A hacker can run a software program system that scans networks and IP ranges, searching for possible weaknesses. When such weaknesses are discovered, the hacker can take more than the machines or infect them, in order to use them as a zombie army” in larger scale attacks.
Prior to the formulation of the Anti-Cybercrime act, as talked about ahead of, all jurisdictions related to cybercrime offenders were left to the decisions of the religious scholar who judged the offense in discretion with the Islamic laws. The Anti-Cybercrime act consists of sixteen articles and is the very first set of laws in the Kingdom of Saudi Arabia created to deal with the expanding threat of e-crime and online criminal activities. These articles clearly define the activities which constitute as cybercrimes and clearly outline the objectives and requirements which the legislation aims at achieving. The act defines every crime and determines the proper penalty in response to each assortment of crime, along with the cooperative enforcement from various agencies. This is completed in order to deal with world wide web crimes and safeguard the national interests in the context of information safety and implementing safe use of computer systems and online networks.